By akshita · January 22, 2026
Your integration platform is right in the workflow for every single patient record, order, and result. It integrates EHRs, lab, billing, telehealth, and analytics systems, which make it among the most vulnerable points for healthcare data security within your organization.
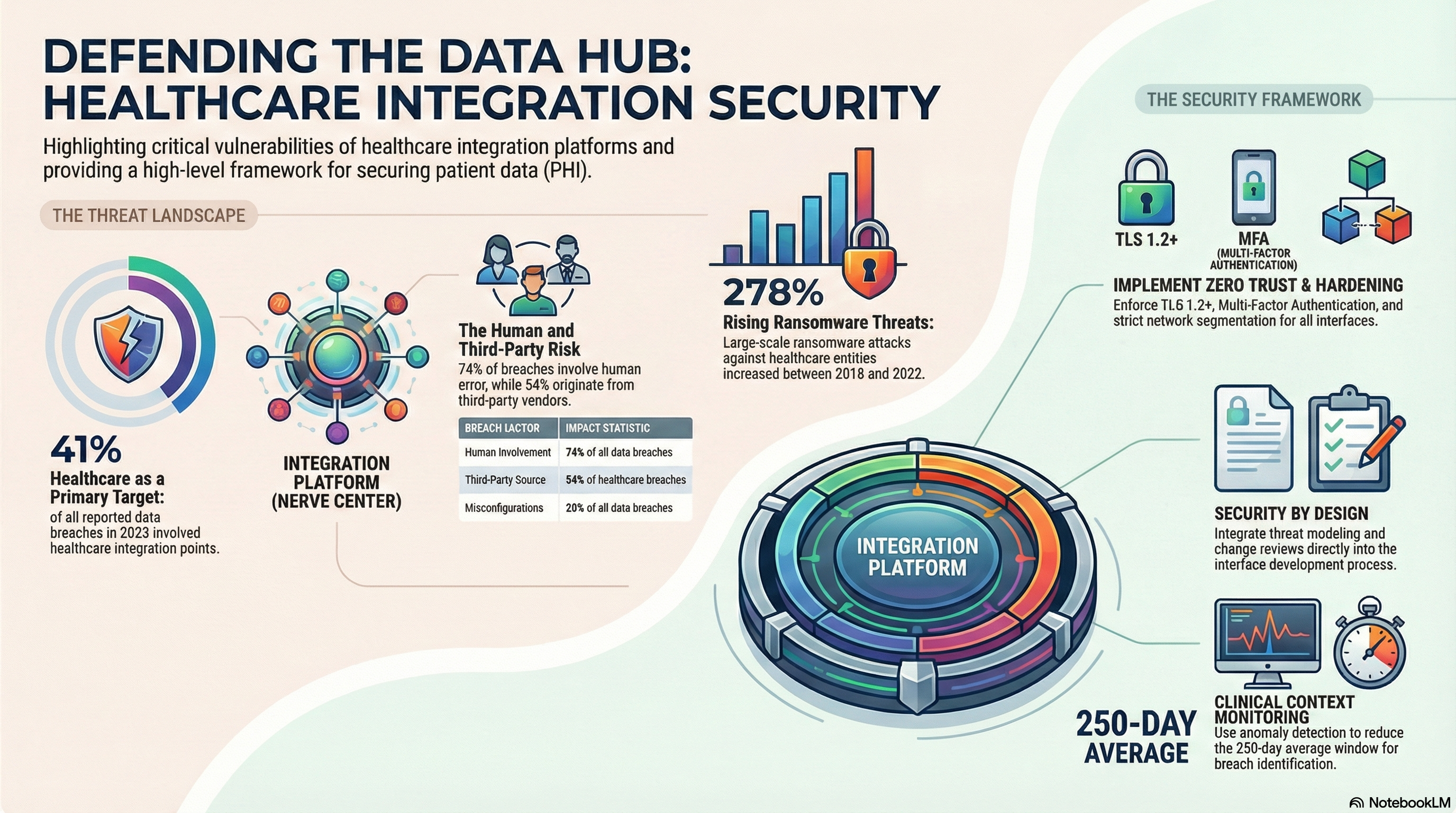
Attackers are well aware of this fact. The area involving healthcare comprised approximately 41% of all reported data breaches in 2023 and often involves the integration. On the other hand, your internal stakeholders are encouraging the quick onboarding of the partners, the data, and automation.
What you want is an approach to integration that is fast-moving yet risk-averse. This means that the security of the integration platform is primary, not an aside. It means integrating the secure transfer of data into how you build, roll out, and manage every interface.
It will take you through effective and high-impact data security measures for healthcare integration platforms. The guide will show you areas of attack interest, areas of greatest importance for controls, and HIPAA secure integration to meet real-world requirements.
Security Threats
Before control design, it is necessary to have an understanding of the threat patterns in the area of healthcare integration platforms. The most common threats are found in a few regular categories.
Compromised credentials and access abuse
The integration engine may contain service accounts with wide system-level access. Using these credentials, attackers gain direct and massive entry points to PHI. As per the 2024 DBIR by Verizon, about 74% data breaches had human involvement, such as phishing and credential attacks.
These might include things like a shared admin login, hard-coded passwords in interface code, or SFTP accounts without multi-factor authentication. Then, once a single account has been breached, it is used to jump between a whole network environment through the integration platform.
Unsecured endpoints and protocols
Legacy health systems use outdated protocols, flat files, and unencrypted connections. If your integration layer accepts these without strong transport protection, you will be exposing PHI over the wire.
The very same risk exists with the use of public endpoints, APIs, and VPNs with broad access. Attackers seek to leverage a poorly configured interface, weak TLS, or an open port associated with integration services.
Third‑party and vendor risk
Your integration platform anchors secure data exchange with payers, labs, HIEs, and digital health partners. Each external connection expands your attack surface. According to a Ponemon study, 54% of healthcare organizations experienced a data breach caused by third parties.
If one partner handles PHI without strong controls, your integration platform is essentially serving up sensitive data into unsafe hands. That risk resides with you, not just with the partner.
Ransomware and data integrity attacks
Health continues to be at the top of ransomware target lists. The U.S. HHS reported a 278% increase in large ransomware against healthcare entities from 2018 to 2022.
Your integration platform is a high‑value target. If it goes down, clinical operations suffer. If message flows get altered or delayed, patient safety and billing are at risk. That means availability and integrity protections are as important as confidentiality.
Essential Controls
The security of healthcare data is enhanced if you consider your integration platform to be controlled infrastructure rather than, by contrast, middleware solutions. This is because these critical security mechanisms represent the foundation of security for an integration platform.
Security by design for interfaces
- Use secure transport protocols for all new interfaces.
* Authenticate and authorize all endpoints.
one. Use interface templates that include logging, error handling, and masking.
- Isolate non-production environments from production environments through network security.
Incorporate security into your interface development process. This involves interface change reviews for security purposes, threat modeling for new data flows introduced by the interface, and patterns for handling PHI.
Network segmentation and zero trust principles
Segment network zones to place integration servers within tightly controlled ingress and egress. Limit communication to specific systems, ports, and protocols. Consider every connection as untrusted unless it is appropriately authenticated and authorized.
Conform to a zero-trust stance. Integration components should validate identity, device posture, and context, not network location. For cloud-based platforms, utilize private connectivity and limit public exposure.
Configuration management and hardening
Use secure baselines for the operating system, databases, and integration tools.
- Turn off unused services and ports.
- Implement stringent password policies and lockout policies.
- Stay current with vendor patches and security notices.
Misconfigurations are still a very close second as a breach cause. A study conducted by IBM revealed that a lack of system configurations or vulnerabilities was the root of 20% of breaches. Hardening and Change Control help to fill such vulnerabilities.
Vendor and third‑party governance
For HIPAA secure integration with third-party providers, consider a risk object for all connections. Ask for security risk assessments, BAAs, and proof of HIPAA compliance. Determine who can share what information and how.
- Keep a list of all data flows and endpoints from external sources.
- Least privilege should be implemented at the interface level and not just at the network level.
- Vendor access should periodically be reviewed.
Encryption & Access Management
Encryption and access control measures play an important part in healthcare security. They safeguard Protected Health Information (PHI) at rest, in transit, and in use.
End‑to‑end encryption for secure data exchange
All interfaces that transfer PHI must implement strong transport encryption. The minimal requirement is now TLS 1.2 or later with secure cipher suites. For file transfers, the only acceptable methods are SFTP, FTPS, and HTTPS—but never FTP or insecure connections.
For static data, encrypt the integration databases, message stores, PHI-containing log files, and configuration backups. HIPAA’s Security Rule requires reasonable and appropriate encryption. Encryption also minimizes the impact of a breach because, in some states, encrypted files qualify for an exemption from a Breach Notification.
Among the top issues, again and again, has been unencrypted devices pointed out by the Office of Civil Rights. It was found in one analysis carried out by HHS that more than 60% of large breaches in the early years of the use of the portal were unencrypted devices either lost or stolen although it is now changing to hacking incidents.
Centralized key and certificate management
This is because poor handling of keys undermines effective levels of encryption. Key management is currently a challenge entrusted to integration platforms, which have to handle certificates, keys, and API keys.
- Rotate keys/certificates on a specific schedule.
- Do not store keys in your code or scripts.
- Limit key access to certain roles and services.
Identity and access management for integration teams
Treat integration admins and developers as privileged users, with the ability to read, route, and transform PHI across systems. Strong identity controls will ensure only the right people access the right functions.
- Make sure that multi‑factor authentication is in place for all admin interfaces.
- Use role‑based access control aligned to job duties.
- Segregation of Duties: Split roles in development, operations, and security.
Record and review all administrative actions.
The core functions include access control, according to the National Institute of Standards and Technology. Identity management is linked to both prevention and detection. NIST’s guidance on access control points out that robust IAM will lower the chances of misuse and increase response times if incidents happen. Both are summarized in their SP 800-53 AC controls.
Fine‑grained access for data and functions
Go beyond admin tasks. Own the following user and service permissions:
- View PHI within message payloads.
- Download logs containing sensitive fields.
- Use or interface with entities that transport PHI.
- Set up external endpoints.
This degree of security of an integrationplatform protects from large-scale exposure in case of misuse of an account.
Monitoring
You enhance the healthcare sector’s cybersecurity when you consider your integration platform a security-monitored resource. Constant observation shifts your interfaces from blind spots to security sensors.
Security logging with clinical context
Logs ought to reflect more than the technological occurrences. They ought to allow you to quickly answer various security questions. In this regard, they ought to provide answers to the following:
- Which external IPs accessed specific APIs containing PHI?
- Who accessed or altered interface configurations?
- Messages with which types of PHI were transmitted unsuccessfully, tried again, and/or redirected?
Sync logs to your SIEM/SOC. Add structured fields like source system, destination system, interface name, message type, and user ID. Hide PHI where appropriate, maintaining enough information to facilitate analysis.
Anomaly detection and alerting
Typical monitoring usually involves throughput and uptime. For healthcare data security, extend this into behavior analytics. Alert on:
Unusual data flows, such as new destinations or large spikes in volume.
- Repeated authentication failures or new administrator logins from unknown locations.
Any unexpected changes in interface configurations or certificates.
According to one study by the Ponemon Institute, the time required for healthcare organizations to identify and contain data breaches is more than 250 days. Better detection around integration flows reduces that window and limits impact.
Operational resiliency monitoring
Security and availability are interrelated. If your integration downtime延迟orders, test results, and/or ADT messages, your risk increases. Also include:
- End-to-end health checks related to key clinical and financial processes.
- Automated testing of integration components regarding failover.
- Capacity and performance thresholds with early alerts.
Greater visibility into operations enables you to detect attacks that attempt to disrupt operations, as well as those that simply exfiltrate data.
Conclusion
Your integration platform is one of the most strategic points at which to strengthen healthcare data security. Every HL7 feed, FHIR API, and batch file either shrinks risk or widens it. The difference lies in how you design, secure, and operate the platform that connects it all.
By focusing on security threats, essential controls, encryption, access management, and monitoring, you move toward a defensible, HIPAA-secure integration approach. You also give your teams confidence to deliver new digital services, partner connections, and analytics without fearing new vulnerabilities.
Strong health care cybersecurity in integration does not slow your roadmap. On a proper foundation, it becomes an enabler of safe, scalable, and secure data exchange across your ecosystem.
Vorro helps healthcare organizations modernize integration with security at the center. Our platform and team focus on the security of integration platforms, HIPAA secure integration patterns, and operational resilience for real clinical and business workflows. If you want to bring your integration strategy in line with your security and compliance goals, talk with Vorro about building a secure, future‑ready integration foundation.
FAQs
What function does an integration platform serve with respect to healthcare data security?
Your integration platform is capable of routing, transforming, and exposing data. This is for PHI, financial, and operational data. Although it is sitting between so many endpoints, it has implications for confidentiality, integrity, and availability. Governance, encryption, and access restrictions and monitoring around the integration platform are crucial to securing data within healthcare.
In what ways is HIPAA relevant to integration platforms?
HIPAA considers your integration platform to be a part of your covered entity or business associate environment. The HIPAA Security Rule states that standards should be applied to protect ePHI using the following areas: Access Controls, Audit Controls, Integrity Controls, and Transmission Security. HIPAA secure integration requires policies, technical measures, and BAAs that include your integration components, interfaces, and third-party connections.
Which protocols are used for secure data communication?
For transport layer security, use TLS 1.2 or later for APIs and web applications, or SFTP or FTPS for file transmissions. For contemporary APIs, use best practices for healthcare from FHIR using OAuth 2.0 or OpenID. For encryption, do not use unencrypted transport protocols such as FTP or unsecured HTTP for any protected health information. Make transport protocol selections consistent with your overall healthcare architecture.
How frequently should access and configurations be reviewed?
Check and review administrative and service accounts quarterly. Verify that users are correctly assigned to accounts and no longer-existing employees or vendors do not have access to accounts. For change management in configuration changes, implement formal change management. Critical interfaces or external points for safe data transmission should be reviewed more regularly, especially after a merger and/or a significant upgrade and/or lessons learned from an incident.
How are the security features and operations of an integration platform evaluated?
Metrics to measure this focus area are the number of high-risk vulnerabilities open for the integration components, mean time to detect/respond to incidents related to the integration, percentage of interfaces that have strong encryption enabled, logging into the SIEM solution implemented, and successful vendor security reviews.
