By akshita · January 15, 2026
Your organization transmits data every minute. EMR updates, lab feeds, clearinghouse transactions, remote monitoring data transmissions, and connectivity to partners and payers. Every connection produces the same question: Is the data integration of HIPAA as strong as the care?
You are pushed from every direction. Patients demand online access. Clinicians demand and need real-time data. Regulators demand seamless security performance. All around, meanwhile, your interoperability platform must deal with technical debt, vendor lock-in, and escalating interoperability requirements.
By adopting HIPAA data integration as an art and not just fixing multiple point solutions, you can ensure less risk, less friction for the clinician, and more interoperability over the long term. This guide helps you develop an understanding of how you can integrate with the privacy principles of healthcare.
HIPAA Overview
It is essential to have a clear insight into the relationship between HIPAA and data exchange before tuning the interfaces or upgrading the integration engine.
What HIPAA Protects In Data Integration
“HIPAA protects individually identifiable health information in any given form or format. It covers all messages and all data in all batches and API transmissions that flow from one system to another. “The Security Rule says that you must protect your electronic protected health information in terms of its confidentiality, integrity, and availability. All three of our case studies involve workflows at the nexus of all three.”
The Security Rule requires administrative, physical, and technical safeguards commensurate with your risk. In an integration scenario, this indicates a need to develop policies regarding the handling of interfaces, sound technical procedures for handling each transport mechanism, or change/incident procedures in the operational area.
The enforcement pressure is not just theoretical because the Office for Civil Rights of the HHS reported more than 4,500 large breaches of unsecured PHI since 2009, with a large percentage of these involving transmission failures, missent files, and insecure endpoints. You cannot consider integration a form of “back office plumbing” in isolation from the issue of compliance.
Key HIPAA Rules That Touch Integrations
Some of the HIPAA regulations that correspond to the practices of HIPAA data integration include:
- Security Rule: Outlines standards for access control, integrity, transmission security, audit controls, and person or entity authentication of ePHI.
- Privacy Rule: Improves the confidentiality provisions for PHI, adding provisions for uses and disclosures for treatment, payment, or operations, as well as for minimum necessary access.
The Health Insurance Portability
- Breach Notification Rule: Involves the evaluation of the incident and the notification of patients when confidential health information is breached through the transfer or at rest.
- Business Associate Agreements: Integration vendors and hosting partners that handle PHI must do business within compliant BAAs that define their security obligations.
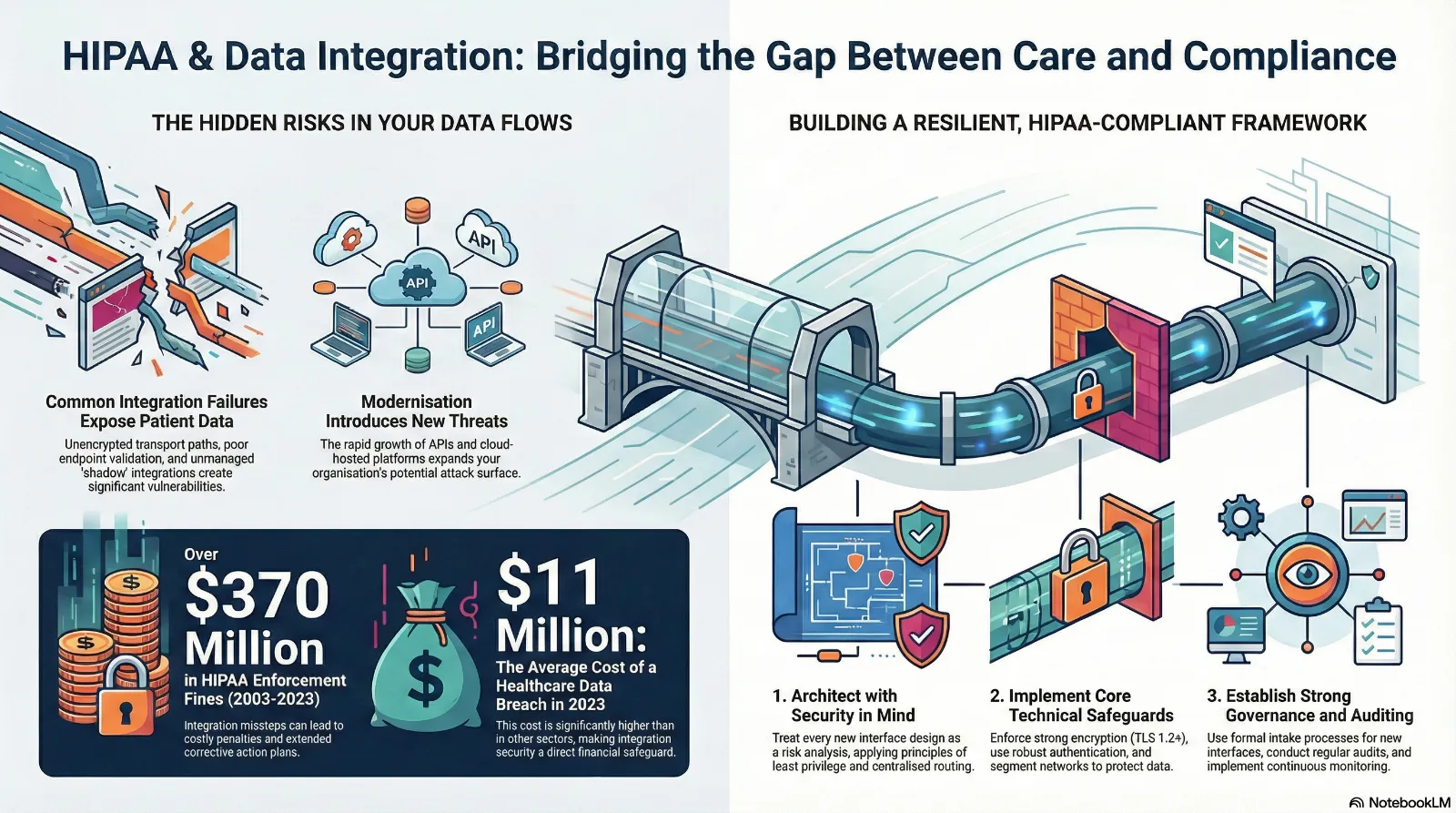
The regulatory expectations are increasing every year. For instance, OCR recovered over 370 million dollars in HIPAA enforcement actions in the period between 2003 and 2023. The misstep in integration places you not just in a position to be penalized but also means extended corrective action plans covering all the new interfaces you roll out.
Integration Risks
You are already investing in EMR compliance, endpoint security, and identity management. Still, most incidents trace back to integration blind spots. Visibility across the full risk profile is critical as you build out a resilient HIPAA-secure data exchange program.
Common Failure Points In HIPAA Data Integration
The following are several patterns that crop up time and again in IT healthcare compliance programs:
- Unencrypted transport paths: Older VPN tunnels, FTP jobs, or internal sockets that transmit PHI without modern encryption or strong certificates.
- Poor endpoint validation: Interfaces that receive or accept inbound feeds from any IPs or accounts with poor controls are ripe for spoofed or misdirected messages.
- Shadow integrations. Ad hoc scripts, unmanaged vendor connections, or “temporary” point-to-point links that bypass your standard review process.
- Poor error handling: Failed messages that sit in plain text queues, shared email inboxes, or unsecured logs while teams are troubleshooting.
- Overbroad routing. Exchanges transmit the whole clinical document even where the workflows demand only a small piece of information. This further reduces the minimum necessary compliance.
Integration complexity increases the risk. On average, a hospital will share data with more than 30 other organizations, and they all have their own data formats and security requirements. Absence of good control and governance models in integration increases your control model risk with every new endpoint.
Risks Unique To Modern Interoperability
“New interoperability rules and digital front door methodologies present new risks to the integration of Protected Health Information under the HIPAA regulation.”
- API sprawl. FHIR APIs and third-party applications extend data sharing access beyond HL7 and batch methods. In a 2023 report issued by the ONC, more than 70% of hospitals leverage APIs to share data with third parties, growing vulnerabilities through misconfigurations.
- Cloud-hosted integration engines. Cloud hosting offers scalability, although there must be close alignment of cloud security mechanisms and BAs with your internal HIPAA safeguards.
- Clinically driven workflows. The use of portals, telemedicine systems, or remote monitoring systems is all connected to the obligation for EMR because data queries your designated reportable data set.
These risks, rather, militate against the argument for the necessity of interoperability. They argue for a rigorous HIPAA-secure data exchange architecture whenever there is a new connection, both as a clinical enabler and a security risk.
Security Controls
Best-practice healthcare IT compliance programs for strong security integrate security into the integration life cycle, as opposed to looking back at it after it happens. You have to have a clear set of compliant controls in place that everyone understands.
Architectural Principles For HIPAA Data Integration
Principles that inform the design of each interface:
- PHI aware design. Consider each integration design review a risk analysis. Determine what PHI is flowing, to where it goes, for how long it is stored, and by whom it can be accessed.
- Least privilege routing. Only transmit those data points that are needed within the workflow process. For example, there is no need for complete notes if only demographic information and coding are needed.
- Standardized patterns. Employ a few standard integration patterns, including safe APIs, SFTP, and proven VPN choices, and maintain consistent security standards.
- Centralized mediation. As many interactions as possible ought to be routed through a central integration platform that enables common authentication, logging, and throttling.
Technical Controls For HIPAA Secure Data Exchange
Apply those principles to specific technology measures:
- Encryption in transit and at rest. Enforce TLS 1.2 or stronger for all external connectivity. Use secure encryption suites for integrated databases, message queues, and file shares. HHS recommendations rank encryption as a significant addressable security control for transmission security.
- Strong authentication. Employ certificate-based mutual TLS or token-based authentication for APIs rather than relying on shared accounts/passwords between systems.
- Network segmentation. Internally integrate the servers in a restricted area of the network with a small number of incoming/outgoing lines and intrusion detection.
- Secure management of credentials. Keep keys and passwords in fortified vaults that implement rotation policies and role-based access.
- Message integrity controls. Protect messages via checksum, signature, and/or message digests from endpoint to endpoint.
- Data minimization and masking. Mask or redact the nonessential identifiers in the log files or test environments. De-identified data should be used in developing the interfaces.
These controls also meet broader industry expectations. For example, the Ponemon Institute reports that the average cost of a healthcare data breach reached abput 11 million dollars in 2023, significantly higher than in other sectors. Integration security is not an isolated task. It is a direct financial and operational safeguard.
Process Controls And Governance
Technology by itself will not prosper if it is not combined with process discipline. Effective build integration governance should start the journey of integrating engineers, security, compliance, and operations teams.
- Formal intake and risk analysis. Route all new interface requests through a formal intake process that assesses data classification, PHI analysis, and security requirements.
- Common templates. A set of design templates and checklists for each integration type, including required encryption, authentication, and logging fields.
- Vendor and BAA reviews: Assess vendors’ security, data residency, and processes for each vendor before signing the contract.
- Change management. Record configuration changes, versioning, and roll-back procedures for all interfaces before deployment with a security check.
- Training. Teach integration engineers and analysts about HIPAA, minimum necessary standards, and secure methods of troubleshooting.
Maturity in governance equals improved results. Companies with strong security process maturity see data breaches occur fifty percent less often than companies with low maturity, despite similar technology. An effective process converts a procedure into a routine.
Audit Monitoring
It’s essential to have continuous insight into the data integration processes to make the difference between a quick containment response and prolonged vulnerability. You want something beyond the logs or the raw data. You want the structured view of the monitored issue or the results of a periodic audit.
What To Monitor Across Integration Flows
An effective approach to monitoring healthcare compliance IT involves the following security relevant signals:
- Connection events. Successful and unsuccessful attempts to connect, failed authentications, certificate problems, and unusual sources of connections.
- Message volume and traffic patterns. Abrupt changes in the number of transactions, irregular sizes for batches of messages, or irregular times, which could reflect misuse or glitches.
- Data Anomalies. Unusual variables, discordant patient identifiers, or incorrect codes that may reflect tampering or upstream issues.
- Error processing paths. Messages that have been moved into dead letter queues or manual processing routes, and details of who viewed and resolved them.
You must synchronize your monitoring process with HIPAA’s standard for auditing controls. The logging activity in the platforms you have integrated must be able to point towards identity information for either user or system identity, time stamp, data sources and destinations, actions performed, and results obtained. The logging activity must be directed towards your SIEM solution or centralized security analytics system rather than being recorded within local files.
Building A Strong Audit Program
Monitoring enables real-time awareness. Audit offers structured hindsight. Both are important.
- Regular Access Reviews. Verify which company accounts and third-party suppliers have been given access to the endpoints of the integrations. In addition, ensure old, unnecessary permissions are deleted.
- Configuration audits. Verify that transport security, cipher suites, and authentication configuration comply with your requirements for all interfaces.
- End-to-end traces. Occasional tracing of sample messages via each integration path to ensure routing, masking, and logging.
- Exercises related to incidents. You can conduct tabletop exercise simulations related to incidents such as misplaced files and phishing vendor accounts.
There is support for such an emphasis from external expectations as well. The HHS Cybersecurity Program indicates that more than 70 percent of recent major healthcare breaches involved hacking or incidents related to IT, and many of these are associated with complex data flows. The best audit and monitoring provides the ability to monitor and act before an attacker can get into the seams in the integration fabric you’ve built.
Conclusion
Data Integration related to HIPAA is where clinical, tech, and regulations meet. Each interface you build or sustain impacts patient confidentiality, provider workflows, and risk. Raising your sights to integrate as a strategic strength will liberate you from reactive problem-solving to proactive resilience.
Excellent programs have common characteristics. They begin with an understanding of the responsibilities under HIPAA. They map and mitigate risks before an incident. They integrate security into design, build, and operations. They treat monitoring and audit as a daily routine, not an annual activity.
You do not have to transform your integration infrastructure overnight. You have to have a plan to determine how you are getting from where you are to where you need to be regarding technology, process, and governance. It must serve to assist you in abandoning your tenuous point-to-point connections, your reliance on workarounds, and your lack of EMR compliance.
Vorro can assist in the modernization of HIPAA secure exchange, simplification of complex integrations, and alignment with healthcare standards for the privacy aspect. If you are now ready to align the strategy for integration with the mission and regulatory requirements, you can schedule a call with the Vorro integration experts.
FAQs
What does HIPAA data integration mean in practice?
HIPAA Data Integration pertains to the safe transfer of PHI from different systems, such as EMRs, lab systems, billing systems, business partner networks, and patient portals. It encompasses all interfaces, messages, APIs, and file transports that convey PHI. This will relate to all the data flows concerning encryption, authentication, access, logging, and Minimum Necessary principles involved in HIPAA compliance.
What are the implications of HIPAA on EMR Compliance for Third-Party Integrations?
A compliance posture regarding your EMR system has to extend across all interfaces that read from or write to your EMR. You have to confirm that all third-party interfaces have a valid Business Associate Agreement, secure transport, meet minimum requirements, and enable logging. Any type of configuration change to your EMR, like new data fields or routing, has to be reviewed for risks before entering production.
What are the initial steps to mitigate integration risks?
Begin with an inventory of all interfaces and data flows that involve PHI. They could include legacy scripts and unauthorized vendor connections. Tag them for the type of data communicated, method of transmission, authentication factor, and ownership. In addition, address those with insecure transports, obsolete software applications, and stubbornly unowned assets next. Establish patterns of operations and apply them uniformly for all new tasks.
How often should a HIPAA secure data exchange occur?
It is important to keep track of the integration events on an ongoing basis and conduct regular audits at least on an annual basis; for high-risk interfaces with external APIs or for large batch exports, audits are done on a quarterly or bi-annual basis. The audits must be risk-associated and not on an annual basis.
How Vorro helps healthcare compliance IT teams?
Vorro brings integration know-how, technology, and skills specifically geared for a healthcare environment. They will assist you in reviewing today’s data flow patterns, designing secure patterns, modifying or optimizing existing interfaces, or enhancing monitoring capabilities, writes Tod das Census-EC team. “Vorro ensures integration designs are compliant with HIPAA, healthcare privacy laws, or your organization’s security policies so that healthcare delivery teams can access information without increasing risks.”
